News & Blog
- All Posts
- Blog
- Career Management
- Computer Security
- Cyber Defence
- Cyber Incidence Response
- Cyber Preparedness
- Cyber Security
- Data Privacy
- Endpoint Security
- Fraud Investigation and Examination
- Fraud Management
- IT Security Audit
- Marketing
- Mobile Security
- Training
- UX/UI Design
- Web Development

When fraud happens, it is never out of the blue. The signs are always there, ignored, excused, or...
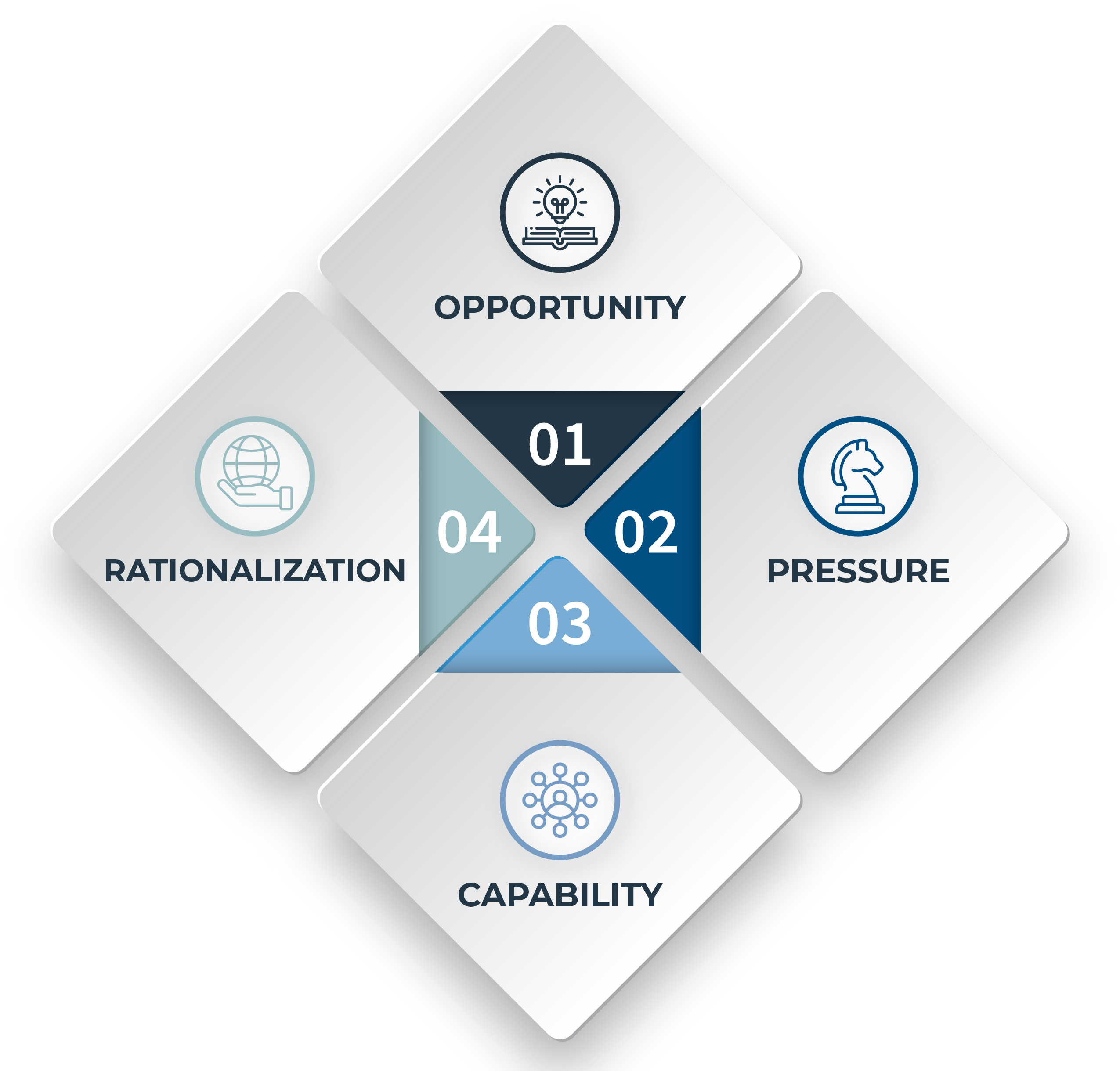
Fraud doesn’t begin with bad people. It begins with pressure. With a quiet “just this once.” With a...

Fraud doesn’t knock. It walks right in through your open doors, process gaps, ignored red flags, and blind...
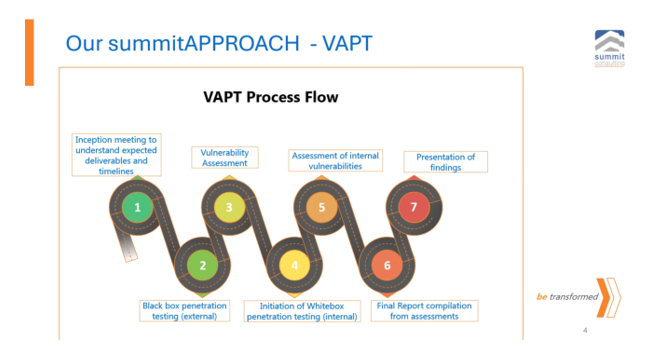
You have a penetration testing process. You have a risk management department. You have an internal audit team....

On 11th February 2025, a procurement officer at a prominent government parastatal in Entebbe signed off an “emergency”...

Everyone loves to preach about “trust.” It is easy. It feels good. It looks good on glossy company...

A padlock on a chicken coop means nothing if the fox has the keys. In a recent cybersecurity...

A monkey tied to a tree still thinks it is free. That is the modern internet user clicking...

The issue is: Time is not money, it is evidence On 26th February 2025, the CEO of a...



